Advanced Internet Solution 2087193276 Details
Advanced Internet Solution 2087193276 Details presents a framework for privacy-preserving data, distributed edge compute, and resilient communication fabrics. It emphasizes modular governance, interoperability, and secure migrations from legacy systems. The architecture aims for scalable deployments, auditing, and rollback plans while managing risk and latency. Its practical value hinges on baseline configurations and validation checkpoints. The topic invites scrutiny of tradeoffs and implementation challenges, offering a clear path forward—yet the full implications remain to be explored.
What Is Advanced Internet Solution 2087193276 Details?
Advanced Internet Solution 2087193276 Details is a term referring to a proposed or hypothetical set of internet-related services and capabilities associated with the numeric identifier 2087193276. The concept outlines high-level objectives and boundaries, focusing on adaptable, user-centric outcomes.
Idea 1: hypothetical architectures.
Idea 2: legacy migrations.
The framing emphasizes structured analysis, minimal fluff, and freedom-conscious clarity for informed decision-makers.
Core Components and Architectural Choices
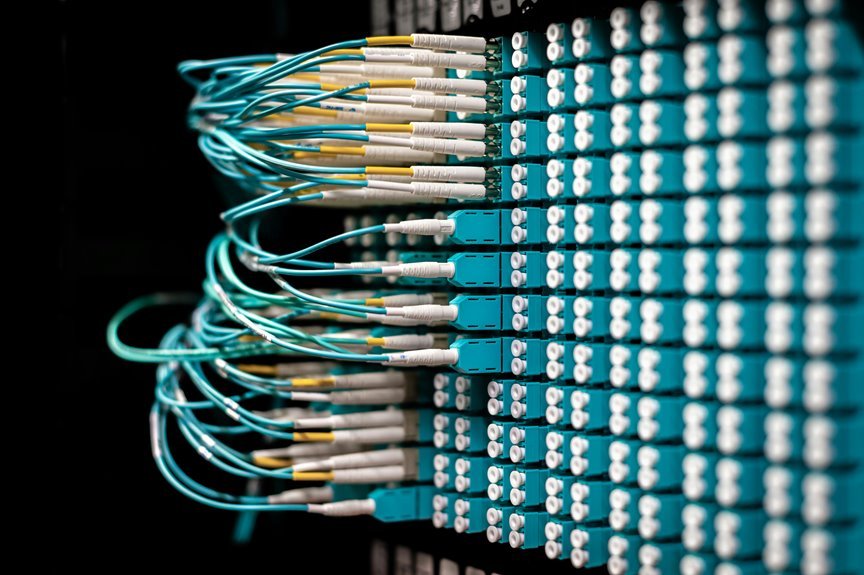
Key components include data privacy-preserving services, distributed edge compute, and resilient communication fabrics.
Decisions balance autonomy with coordination, prioritizing security, interoperability, and maintainability.
This framework enables adaptable deployments while preserving freedom, transparency, and effective governance in complex networks.
Real-World Benefits: Speed, Security, and Scalability
The real-world benefits of the described architecture emerge from its modular, privacy-preserving services, distributed edge compute, and resilient communication fabric.
It delivers speed optimization through localized processing, reducing latency while sustaining throughput.
Security hardening is integrated at every layer, decreasing exposure and improving threat resilience.
Scalability remains proactive, enabling elastic resource expansion without compromising performance or user autonomy.
Deployment Steps and Common Pitfalls
Deployment steps must be followed with discipline to ensure consistency and reliability. The process outlines baseline configurations, validation checkpoints, and rollback plans, while documenting decisions for future audits. Attention to insight gaps clarifies assumptions and informs risk mitigation strategies.
Potential pitfalls include scope creep, incomplete testing, and insecure defaults. Structured reviews, automation, and clear ownership reduce failure modes and support resilient deployment outcomes.
Conclusion
The Advanced Internet Solution 2087193276 details articulate a modular, privacy-preserving, edge-enabled framework that harmonizes autonomy with coordinated governance. Its distributed compute fabric, baseline validation, and rollback plans enable secure, scalable deployments while preserving interoperability. An intriguing statistic: edge computing can reduce latency by up to 50% for many applications, underscoring throughput gains. The design emphasizes auditability, proactive risk mitigation, and transparent governance to sustain resilience, security, and performance across evolving network landscapes.




